Gopala Krishna Behara, Sr. Enterprise Architect, Wipro
Madhusudhana Rao,Principle Consultant, Wipro
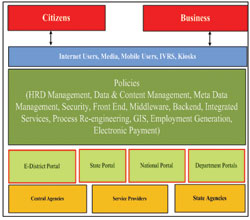
Introduction to e-Governance Policies
The aim of e-Governance is to transform the Government into a knowledge society and make the benefits of information technology available to all citizens.
Government is committed to build people-centered information society, where everyone can create, access, utilise and share information, and which enables individuals, communities and people to achieve their full potential in promoting sustainable development. This can be achieved by setting up the standards/policies for the e-Governance.
The objectives of the e-Governance policies are improving economy, employment creation, citizen-centered governance, and globally competitive government.
This paper consolidates the purpose of various components and the policies to be adapted for achieving better e-Governance based on the author’s experience on national/state government portal and e-District Portal work. The following component policies have been highlighted and articulated in this paper: Human Resource Development & Management, Data and Content Management, Meta Data Management, Security, Front End, Middleware, Back End & Department Automation, Integrated Services, and Process Re-engineering.
Human Resource Development & Management Policies
Human Resource Development for government portal (national/state/e-district) includes building training programmes in e-Governance for IT qualified manpower. It creates awareness among the portal stakeholders and users through sensitisation, orientation and motivation. It provides individuals the necessary competence and increases their work effectiveness through skills training and transfer of knowledge.
The training programme for policy makers and CIO’s should be based on specific IT modules in projects as well as on general IT skills so that they can support the capacity development of the government portal and its integrated departments. Simultaneously, individual participants also need to be trained to meet the portal’s capacity building objectives. The training programmes should be demand oriented and custom tailored, catering to the thrust area activities under the government portal.
Data & Content Management Policies
Policies for data and content management address what kind of content can be included in the portal, formats in which they can be added, attributes and type of information to be provided for each content element and their review and exit policies, etc.
A web based secure Content Management System (CMS) needs to be developed, to facilitate contribution of content for the portal. Each user of the CMS is provided with a User ID and a password to access the CMS modules. Authorised CMS users are grouped into different classes and each class of users are assigned specific roles and access to content categories.
Content should ensure a unified picture of the government information and be up-to-date along with periodic reviews. Content categories are accompanied by the Meta Data, source and the validity date. Documents, schemes, services, forms, websites and contact directory need to be reviewed as per the Content Review Policy. Care should be taken to archive the content that has expired.
Documents, schemes, services, forms, websites and contact directory need to be reviewed as per the Content Review Policy.
Metadata Framework Policies
Metadata is structured information that describes, explains, locates, retrieves, uses or manages an information resource. Metadata standard can be used to classify and categorise portal information and services. It allows identification of services and information intelligently. It helps in inter-departmental information exchange.
Metadata should be independent and flexible to meet the information retrieval and records management needs of any information held in any format. It should also meet the information retrieval and management needs of citizens. The standard must be readily applicable by those with varying experience of preparing resource descriptions. It should be compliant with e-Governance standards and policies, such as the Government Data Standards Catalogue. It should be stable and extensible. The Content Management Metadata scheme should minimise the need for rework of existing products.
 Security Policies
Security Policies
A security policy is a set of rules stating what is permitted and what is not permitted in a system during normal operation. The security policy helps in achieving reliable and stable administration.
The documents that are sent across the network can be of sensitive nature like result cards, land records, certificates, etc. Digital signature is used to verify the identity of the sender. Care should be taken to verify the authenticity of the message and the claimed identity of the message. Information should be encrypted and decrypted to protect it from unauthorised use. It should be verified whether information that is received across the network is the same as that was sent. There should be no scope for any changes like deletion, addition or any other modification when the document is sent or received. Overall, digital signatures are used to settle the integrity of the message. Data and transaction security ensures the privacy and confidentiality in electronic messages through cryptography. Policies should also address Password Schemes, Biometric System, Smart Card Authentication, etc. Firewalls should be used to control and monitor all traffic that flows across the network.
Policies for Front-end
A policy on front-end should include policies related to front-end services like CSC and integrated service centers. The decision on front-ends range on several options like Citizen Service Centers, e-kiosks, home PC’s etc. It addresses how services of a government portal can reach the intended beneficiaries in a cost-effective manner.
CSC’s can serve as a front-end for most of the government services for a nominal fee as they are broadband enabled, connecting rural citizens through the Internet. Mobile phones are also another option.
 Policies for Middleware
Policies for Middleware
A policy on middleware addresses policies related to government portal, gateway middleware, data centers, ownership of VPN’s, and inter-connection.
Acting as a nerve centre, the gateways can handle large number of transactions across the entire network, provide a common set of specifications, and a single point access for departments.
Standards based messaging and routing switch ensures secure and guaranteed delivery of services between the front-end portals and the back-end departments and also intra-department. The back-end departments can be de-linked from the front-end service delivery mechanisms. Infrastructure can eliminate the need for departments to have multiple linkages with various SCA’s providing citizen services through the CSC’s. Each department will connect only once to the middleware and transact with multiple CSC’s. It can capture audit logs and time stamping of transactions going through the middleware, while
also supporting shared common services like authentication, payment gateway, interface, etc.
Policies for Back-End & Department Automation
A policy on back-end includes policies related to the broad issues of service provision, to establish clear guidelines to distribute IT equipment and provide IT services to users based on written request.
Data collected by or for a government agency under statutory provisions or by contract or through an information-matching agreement under the Privacy Act, is owned by the government, not the individual agency. A Data Administrator should be appointed with a government-wide mandate to manage and develop the portal data and document assets in accordance with established policies and standards.
Every item of data and every business document held by or maintained for a government portal should have a Business Custodian and a Physical Custodian. Access rules should be based on the principle of public and equitable access to information unless explicit reasons preclude this.
Data and business documents need to be managed to preserve and demonstrate their authenticity, integrity to meet business and statutory requirements. Data elements and business documents must be defined in a consistent manner and stored in a consistent format across all stores. Data and business documents need to be managed within a defined retention process.
 Policies for Integrated Services
Policies for Integrated Services
Integrated Service Delivery is regarded as the logical objective of e-Governance. In many cases, the policies are implemented through the delivery of services to citizens, businesses and other entities.
There is a need to define the service levels for various services and identify the processes that need to be changed or re-engineered to meet the defined service levels. The service delivery channels in place should be included to meet the service levels. There should also be some engagement with the citizen both in the definition of the requirement (what service) as well as the delivery mechanism (how it works). Agencies should offer the same service in a common manner, sharing data definitions and at best sharing data, but excluding technological integration between the services. Services should not be inherently integrated, or even with a common look-and-feel, but should be grouped to aid discovery and promote comprehensive completion of necessary services. Specific services should be provided by the agent with the integration being hidden from the customer (eg: two department operations).
Services should be technologically integrated into a pseudo-supply chain application. They should be inter-operable and address cross jurisdictional service delivery. Service needs to meet the citizen’s expectations in terms of speed, transparency, affordability, reliability, and accessibility, etc.
Process Re-engineering Policies & Frameworks
Lot of services are used for business operations of the government. The IT services need to be allocated to users based on business requirements and relevant authorisation.
Process re-design, is the critical analysis and radical re-design of work flows and processes within and between government departments.
Review should also be undertaken of the Objectives and Performance Metrics of the services in comparison with the current level.
Assessments should also be carried out regarding whether deficiencies in service metrics can be met through changes in the current set-up, especially those relating to centralised data availability, process points, functions and tasks performed and delegation of power at each of these points, and so on.
The re-designed processes should be enabled and implemented with appropriate changes by way of amendment to the rules, acts, administrative orders, etc. Demand for targeted services, estimated adoption rate and revenue must also be estimated.
The levels for each offered service should be evaluated and a methodology for continuous measurement and reporting should be proposed. Explanation should be given on various categories of risks which are most likely to impact the performance of delivery of services. Process re-design must clearly detail out the proposed channel for delivery of services and plan for integration with the CSC scheme.
Sensitive information should be protected from unauthorised disclosure or intelligible interception. Care should also be taken to safeguard the accuracy and completeness of the information.
Be a part of Elets Collaborative Initiatives. Join Us for Upcoming Events and explore business opportunities. Like us on Facebook , connect with us on LinkedIn and follow us on Twitter, Instagram.
"Exciting news! Elets technomedia is now on WhatsApp Channels Subscribe today by clicking the link and stay updated with the latest insights!" Click here!