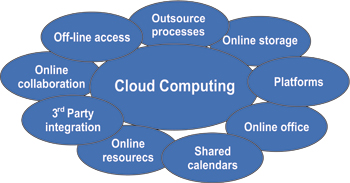

There is a lot of buzz in the media about ‘Cloud Computing’ and how it will – or is, dependent on your viewpoint – transforming large scale enterprise systems in the private sector. The Cloud, like so many concepts is not entirely new, but rather a confl uence of existing and new technologies. An excellent primer was published last year by the School of Electrical Engineering and Computer Sciences, UC at Berkeley, (see http://www.eecs.berkeley.edu/Pubs/ TechRpts/2009/EECS-2009-28.pdf ) but as with any academic report it, can get ‘a bit complex’, so here I would like to address a somewhat simplifi ed outline of Cloud Computing and its application to government.
Before we can address what it may do, we really need to understand what Cloud Computing is all about, after all we have the Internet, isn’t that the Cloud? SAP for example, has described the Cloud simply as the ‘Future Internet’. The CEO of Oracle says that Cloud Computing is just ‘a redefi nition of what his company already does’, while Open Source advocate, Richard Stallman cautions about proprietary IP concerns via the cloud.
So it’s not quite so simple. The elements of the Cloud have been gathering for a while; the long held dream of computing as an ‘on demand – always available ‘ service, is a promise that like electricity, you turn it on and turn it off and get charged for your exact consumption. A neat idea after all we don’t all own a power station (yet – but personal solar is gaining in many countries) but we want ubiquitous, reliable and overall, cheap power.
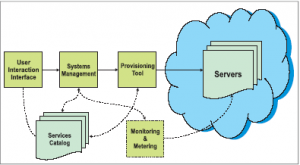
Dr. Peter Mell and Tim Grance at NIST1 have defi ned Cloud Computing as comprising fi ve distinct components; On-demand Self-Service: A consumer can unilaterally provision computing capabilities, such as server time and network storage, as needed automatically without requiring human interaction with each service’s provider.

Broad Network Access: Capabilities are available over the network and accessed through standard mechanisms that promote use by heterogeneous thin or thick client platforms (e.g., mobile phones, laptops, and PDAs).

Resource Pooling: The provider’s computing resources are pooled to serve multiple consumers using a multitenant model, with different physical and virtual resources dynamically assigned and reassigned according to consumer demand. There is a sense of location independence in that the customer
generally has no control or knowledge over the exact location of the provided resources but may be able to specify location at a higher level of abstraction (e.g., country, state, or datacentre).Examples of resources include storage, processing, memory, network bandwidth, and virtual machines.
Rapid Elasticity: Capabilities can be rapidly and elastically provisioned, in some cases automatically, to quickly scale out and rapidly released to quickly scale in. To the consumer, the capabilities available for provisioning often appear to be unlimited and can be purchased in any quantity at any time.
Measured Service: Cloud systems automatically control and optimise resource use by leveraging a metering capability at some level of abstraction appropriate to the type of service (e.g., storage, processing, bandwidth, and active user accounts). Resource usage can be monitored, controlled, and reported providing transparency for both the provider and consumer of the utilised service.
Grid Computing, as promised by major vendors including Oracle, was to enable the linking of mainframes/servers with essentially dumb clients to centralise processing and storage, and was thus component one and two of the above. This was initially on dedicated hard connections and really was a combination of applications and storage, with usually ownership of apps and storage being with the same vendor.
However, the difference with the Cloud is the ownership of the disparate parts and the application of ‘on demand computing’ to the equation, via the ubiquity of the high-speed Internet. The Cloud addresses the sort of problems that plagues,for example, public transport systems; one of matching capacity with
demand at any particular point in time. In order to cater for peak hour demand – the rush hour – transit systems typically have to own a greater number of buses, trains, etc than they actually need for their overall 24 hour traffi c load; they can scale but don’t have elasticity to manage demand any other way. Ideally their infrastructure would evenly run at 100% capacity over a full 24 hour period.
This however is not practical, hence overcapacity/underutilisation of their investment leading to an increased fi xed capital base that has to be paid for by the public and amortized to recoup costs.
With information processing however, this may be addressed differently by using a now common, underlying ‘on demand’ infrastructure – broadband or high-speed Internet – which may be used by multiple customers – both private sector and public, simultaneously in a multi-tenanted environment that is infi nitely scalable. Each user accesses applications and storage either directly (Private Cloud) or through a hosted contract with a vendor (or vendors) and uses applications on a utility model, sometimes called Software as a Service (SaaS).
Examples of this are SalesForce.com whereby not only users, but usage is charged on a distinct unit basis. In the non IT world, NetJets provides a similar service for the use of private aircraft; the use of the asset but not the ownershipbased on a time/usage billing system.
The Cloud therefore is the realization of the past promise of Grid computing being delivered as a reliable, scalable business – but focuses on tasks and outcomes rather than raw number crunching, that may be used by IT consumers seamlessly in the same manner as desktop or server computing. The objective being the user cannot differentiate but just runs their business as usual without the ownership costs of the apps and storage.
THE ISSUE OF SECURITY
It is important to note that from an OCA perspective, the Cloud can increase overall security since Cloud is an improvement on the status quo. The current position in many environments is one of weak internal physical security controls and people regularly leave security doors open, loose USB sticks, disks, handbags, cell phones, laptops etc on a regular basis. There are many
cases where this has been a signifi cant issue in the real world
 From a software security perspective, typically, fi rewalls and software security in the current environment is imperfect and often inventories of hardware and software are not kept up to date and with mergers and acquisitions in the private sector and department consolidation and shared services in the Public, that means that software security is a moving feast and again imperfect.
From a software security perspective, typically, fi rewalls and software security in the current environment is imperfect and often inventories of hardware and software are not kept up to date and with mergers and acquisitions in the private sector and department consolidation and shared services in the Public, that means that software security is a moving feast and again imperfect.
One basic characteristic of Cloud Computing is that the storage is taken off the client premises; the responsibility for security is something that is down to the cloud service provider. By taking storage off client premises this reduces the opportunity for both physical loss of data, and since the data is stored in the cloud it can always be found. For example, loss of a laptop may involve loosing non-backed up data; a Cloud service means that does not happen (depending on the specifi cation of the service). Thus, risk may be better managed using a cloud service.
VENDORS COLLABORATING
Collaboration between vendors is further enabling the elasticity of the underlying infrastructure. Recently IBM and Juniper Networks announced a means of sharing and migrating workloads over private and public Clouds enabling customer’s existing datacentres to seamlessly interact with the public Internet, using a hardware-based approach based around any-to-any (multipoint) connectivity in conjunction to a Multi-Protocol Label Switching (MPLS) data-carrying mechanism. However, such collaboration may lead to interoperability issues unless standards are agreed upon and the resulting API’s made available under a RAND or royalty free basis.
Microsoft’s recently announced Azure platform is a set of initiatives that enables applications to be accessed and delivered that reside in the Cloud in combination with an enterprise’s current local systems. It is currently under test by early adopters. Such a hybrid may have application with government legacy systems.
TAKE UP IN ASIA
According to a recent IDC survey of IT executives in the Asia-Pacifi c region, 41 percent said they were using or evaluating Cloud based services such as SaaS, but 17 percent said there were currently insuffi cient Cloud services to make the platform a compelling option. More than 50 percent of respondents using such services said cost cutting was the main reason behind their adoption of Cloud Computing so they could reduce their fi xed infrastructure costs.
Another research fi rm, Gartner also noted that the absence of any license costs in advance for SaaS apps may be attractive, but total cost of ownership may be more expensive over time since the costs are usually constant throughout the product’s lifecycle. Globally, a consultancy, Avanade, surveyed 500 U S based C-level executives and reported concerns around Cloud Computing that included security and loss of control, then the challenges of integration with legacy systems, high ongoing costs and poor support.
However, they did recognize that the Cloud presented an opportunity for lower upfront costs and ongoing costs, but in the current economic downturn of the business cycle, were not embracing it; only 27% who were currently using Cloud Computing said that they would increase usage in 2009.
Another issue is availability, which is dependent on the physical Internet structure and its addressing systems, in particular as we move over from IPV4 to IPV6, as well as the reliability of the service providers of the SAAS apps. The well publicised failure of Google’sGmail system for two-and-a-half hours on February 24 has focused attention on availability/reliability issues.
ISSUES SPECIFIC TO GOVERNMENT
Apart from the forgoing, which is applicable to both the private and public sector, government has additional demands in that its IT systems are part of the ultimate cultural history of the nation. In addition, government has to interact with both citizens and business in formatsand protocols that do not verly add an additional burden or expense. So with respect to storage apability, it is probable that for critical lifelong data storage, that government will continue to manage their own data centres for essential records; land titles, court records, census and statistics, possibly medical and pension data, in general. However, some functions such as payroll and HR (or pensions) may be managed using Cloud-based SaaS systems, as well as non critical (read Defence and Diplomatic) communications systems, such as hosted email services.
Privacy and security are no more or less of a concern with the Cloud that with any other distributed data system, however an additional layer of security may be required for certain data such as medical records in the Cloud to gain public trust and acceptance in the near term. In conclusion, like the technologies that came before it, Cloud Computing is a confl uence of innovations that will over time penetrate every aspect of both public and private life, just as the Internet has. Governments need to actively monitor the collection of technologies that make up the Cloud; pilot and evaluate ,do the math and then migrate services as
appropriate.
MICHAEL MUDD
 Mike Mudd (mmudd@ opencomputingalliance.org) is the Chief Representative of the Open Computing Alliance in the Asia –Pacifi c region, based in Hong Kong. The OCA seeks to encourage productivity, growth and employment through new opportunities arising from distributed and networked computing. (www. opencomputingalliance.org)
Mike Mudd (mmudd@ opencomputingalliance.org) is the Chief Representative of the Open Computing Alliance in the Asia –Pacifi c region, based in Hong Kong. The OCA seeks to encourage productivity, growth and employment through new opportunities arising from distributed and networked computing. (www. opencomputingalliance.org)
REFERENCE: http://csrc.nist.gov/groups/SNS/cloud-computing/cloud-def-v15.doc
TCS SOLUTION WINS PLATINUM ICON AWARD IN THE INNOVATIVE USE OF TECHNOLOGY CATEGORY
Tata Consultancy Services (TCS), a leading IT services, business solutions and outsourcing fi rm, has won the Platinum Icon Award for Innovative Use of Technology, the highest award in the category, at the Web Ratna Awards, 2009, for developing the Tsunami Early Warning System (TEWS) for Indian National Center for Ocean Information (INCOIS). The Web Ratna Awards have been instituted under the ambit of the National Portal of India (http://www.india.gov.in) to promote innovative e-governance initiatives and to give due recognition to the exemplary efforts in this direction.
The Tsunami Early Warning System was envisioned as a National Importance E-governance Project by the Ministry of Earth Sciences, Government of India after the 2004 Tsunami disaster. TCS was chosen to develop and implement the TEWS for INCOIS as part of the National Tsunami Early Warning Centre at Hyderabad. A fi rst-of-its-kind implementation in the Indian Ocean Region using state-of-the-art IT and geospatial technologies, the solution provides real-time seismic data to INCOIS scientists helping them detect, assess and monitor Tsunamigenic earthquakes and issue Tsunami alerts. TCS leveraged its quality framework and project management methodologies and experience in designing geospatial solutions to operationalise the system in a record time of eleven months.
Dr Satheesh C Shenoy, Director, INCOIS said, “The award is a recognition of our endeavour to leverage the benefi ts of technology to mitigate potential treat to life and property from Tsunami in the Indian Ocean to nearly 400 million people of our population.” He further added, “The system has proved to be extremely effective in the wake of several high magnitude undersea earthquakes in the Indian Ocean region. We have successfully used the TEWS to validate several earthquakes since inception in October 2007 including the most recent earthquake in April 2010 off southern Sumatra.” INCOIS was able to validate the April 2010 earthquake within 10 minutes and issue Tsunami alerts for Andaman and a Tsunami watch for main land in the next 20 minutes. Tanmoy Chakrabarty, Vice President & Head, Government ISU, TCS said, “As the largest IT-company in India, TCS has always focused on using its core competencies to drive large-scale societal impact and transformation. The Tsunami Early Warning System for India is a robust and versatile solution that can also be leveraged by all countries that are prone to threats from Tsunamigenic earthquakes.
Be a part of Elets Collaborative Initiatives. Join Us for Upcoming Events and explore business opportunities. Like us on Facebook , connect with us on LinkedIn and follow us on Twitter, Instagram.
"Exciting news! Elets technomedia is now on WhatsApp Channels Subscribe today by clicking the link and stay updated with the latest insights!" Click here!