The PURA “Providing Urban-amenities to Rural Areas” initiative in India, as part of the 2020 Vision and the Next Generation National Identity Solutions (aka., Identity enabled National Networks) that are emerging today to fulfill the IT and Communications needs within the PURA context, is a strategic initiative that has the potential to empower Rural India and can ensure that India, in its entirety, can participate in economic and social progress in the next 10 to 15 years. The idea is to connect all of rural India with 5000 such projects at a cost of 50 to 150 crores for each project
Introduction and overview
This paper explores the different perspectives from which Architectural Integration and Functional Alignment can take place, between the PURA “Providing Urban-amenities to Rural Areas” Initiative in India, as part of the 2020 Vision and the Next Generation National Identity Solutions (aka.,Identity enabled National Networks) that are emerging today to fulfill the IT and Communications needs within the PURA context.
PURA is a strategic initiative that has the potential to empower Rural India and can ensure that India, in its entirety, can participate in economic and social progress in the next 10 to 15 years. One key characteristic of PURA is the 30-60 km of ring road connecting a cluster of villages along with a link to a nearby city. For example there are more than 100 villages near a place called Dhamal in Kancheepuram, Tamil Nadu a town that is about 100km from Chennai a Major City in South India. The proposed PURA initiative will essentially connect these villages around the town of Kancheepuram with a circular ring road (2 lanes in each direction) and will connect to a link road (or a National Highway) that connects Dhamal to Chennai.The idea is to connect all of rural India with 5000 such projects at a cost of INR 50 to 150 crores for each project. Dr. Abdul Kalam in his speech at the VISION 2020: PURA As Growth Centers,Workshop held at New Delhi, IIT, in November 2005, articulates and elaborates on 5 types of CONNECTIVITY:
• Physical Connectivity (ring road connecting to National Highways)
• Electronic Connectivity (interconnected Wireless networks)
• Knowledge Connectivity (e-Learning, internet based educational programs, etc.)
• Social Connectivity, and,
• Economic Connectivity
 Along the lines of providing the physical connectivity, there are also plans to provide electronic (Network) connectivity to this Cluster of Villages within a 30 to 60km range. India already boasts fiber networks in all major cities such as Delhi, Mumbai, Calcutta, Chennai, Bangalore and more. Therefore the ideal cost effective implementation of small metrosized networks (50 to 80km range) that would cover these cluster of villages wireless, will involve Next Generation Wireless Networking technologies, such as WiMAX 802.16 and 802.20 (high throughput, high speed 40MBps and low cost) that also leverages existing Internet Connecting wire-line implementations such as Cable and Fiber Optic networks.
Along the lines of providing the physical connectivity, there are also plans to provide electronic (Network) connectivity to this Cluster of Villages within a 30 to 60km range. India already boasts fiber networks in all major cities such as Delhi, Mumbai, Calcutta, Chennai, Bangalore and more. Therefore the ideal cost effective implementation of small metrosized networks (50 to 80km range) that would cover these cluster of villages wireless, will involve Next Generation Wireless Networking technologies, such as WiMAX 802.16 and 802.20 (high throughput, high speed 40MBps and low cost) that also leverages existing Internet Connecting wire-line implementations such as Cable and Fiber Optic networks.
Along with a potential National Interconnected Network deployment, one amongst the first Infrastructure Services that needs to be thought out for multiple reasons including Security, delivery of user centric eGov Services, Context and Profile sharing, etc., is a National Identity System that covers India’s Billion Plus Identities. This type of Identity enabled Network is viewed as the Glue between Services and Access Networks. There are many approaches to a National Identity program, including a Federated model, which is well suited in a distributed network, for; AAA (Authentication, Authorisation, Accounting) Services, Federated access control to Services, OSS/OAM (Operations Support Systems/Operations Administration and Maintenance) Services, NG IN (Next -Gen Intellegent Networks) Services,IMS (Information Management System) How it works- Identity Manager/Sensory Network Services, Programmable Event based Services and more.
This paper discusses the relevance of such a National Identity Infrastructure for electronic connectivity, from a PURA context.
• National Interconnected Wireless Networks (in conjunction with the PURA Initiative)
• National Identity Initiative (in conjunction with the PURA initiative)
• National Converged Architecture -Telecom/IT (inconjunction with the PURA initiative)
• National e-Services Platform -SOA based SDP (in conjunction with the PURA initiative)
• Network Driven eServices (in conjunction with the PURA
initiative)
How does IdentIty systems work?
An Identity System is considered the glue between Networks, Services, Resources, Devices and Users. It ensures that Secure Access to Services and Information Resources are made possible transcending boundaries, including Enterprises/Business Entities, Networks, Domains, etc., for Users from Multiple Devices.
An Identity system consists of four parts:
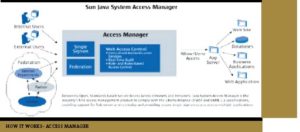
• An Access Management (that includes Federation Management)
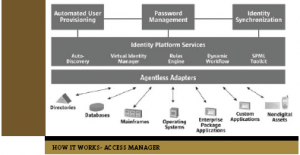
• Identity Management (that includes key and certificates Management)
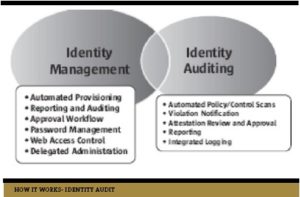
• Identity Auditing (that includes Security event Modeling)
• Identity Repositories (that is typically distributable and holds data about users and policies)
The Access Manager primarily handles Authentication, Authenticated Sessions, executes Access Control policies, federated access control to Services and Web sites, Federated/policy driven profile sharing, etc. The Identity Manager handles the user provisioning, password management, id synchronization, workflow, rules engine, etc. The Identity Manager is more Resource Facing whereas the Access Manager is more Network facing. The Identity Auditing tool collects the audit logs from access manager, federation manager, identity manager, identity agents, adaptors, etc., in centralised and consolidated manner and performs functions such as automated policy and control scans, violation notifications, attestation reviews and approvals and reporting. The Security event modeling capability of this tool running on an near real-time application server, offers observeability of whats going on in a Network at a given point in time. Custom policies can be created to check for examples on anomalies and physical to logical security event correlation, etc.
Last but not the least is the Identity Repository, which generally is a combination of a Large RDBMS (Relational Database Management System) solution and a Network Directory Solution, where a Central repository is used by Identity Manger and Identity Auditor to perform its functions, a distributed repository is used by access manager and federation manger The overall System is deployed in a Federated manner, wherein, each Identity Service Provider creates a Circle of Trust of Domains offering Services and federating between multiple Identity providers.
 An Identity System is critical for various functions today in an Enterprise and Government, that are offering eServices, that includes; Compliance with Auditing Regulations (pertaining to Health Care, Finance, Govt., regulations, etc.)
An Identity System is critical for various functions today in an Enterprise and Government, that are offering eServices, that includes; Compliance with Auditing Regulations (pertaining to Health Care, Finance, Govt., regulations, etc.)
• Access to Services Transcending Business and State boundaries
• Delivery of Converged Services (Voice. Video and Data)
• Delivery of Web Services (Federated Orchestration)
• Reach outs to Access Networks and Access Devices Securely managing and delivering Consumer Profiles (health, voting rights, etc.)
• Securely delivering context
• Identity based Payment, Location, Presence, etc.
• Identity based Devices, ESB (Enterprise Service Bus), ILM (Info Lifecycle Managementt), DRM (Digital Rights Management) and other infrastructure services and is expected to Support standards coming from Project Liberty and OASIS, within the Identity Space -such as SAML (Security Assertion Markup Language), SPML (Service Provision Markup Language), XACML (Extensible Access Control Markup Language), etc.
Requirements for the Deployment of a National Identity Program (& a Identity enabled Network)
• Cooperation between IT, Telecom and Government organisations for multiple pilots – between 4 or 5 in potential locations in the North, South, West, East and Central India, closer to major cities. In conjunction with the deployment of Wireless Networks and e-Services (Identity is the Core Infrastructure Service Building Block that Glues Service to be delivered via a Network to Users).
 • Common Infrastructure SW Services (open source) per PURA cluster of villages or multiple PURA– customised with location specific information, entertainment, education, news, etc. (based on requirements captured from local regions)., for example, one region might have a heavy concentration of cotton production and clothing
• Common Infrastructure SW Services (open source) per PURA cluster of villages or multiple PURA– customised with location specific information, entertainment, education, news, etc. (based on requirements captured from local regions)., for example, one region might have a heavy concentration of cotton production and clothing
manufacturing,and there specific needs have to be met in terms of information services.
• Potential Identity Service Providers per Indian State – that acts as the IDP for the few 100 PURA’s (creating a Circle of Trust between the PURA’s) per State- interconnecting these State IDP’s in a federation Model.
• Requirements around Identity enabled WiMAX Networks, similar to; http://www.prontonetworks.com/ SunProntoWiFiPaper.pdf
• Open Source Software platform that supports open standards.
• Assessment of hardware and software costs and requirements based on the 5 Pilots (web servers, application servers, security requirements, and more).
• Assessment of networking requirements and costs between W-MAN and NAP’s (Network Access Protection) located in cities (T1, T3, fiber link, etc.)
• Assessment of administrative staff requirements and cost of such human resources to augment network deployments per location, based on Pilots.
• Vendor participation and funding for trials (in terms of network equipment, hardware and software tools) with assistance from the Indian Government and Educational institutions (approximately USD 2.5 million for 5 trials)
• Defined set of implementable Security functions and Policies
• Services that require Federated Access
High Level conceptual architecture
India has a total of 3.3 million square kilometers of land area that requires network coverage. Roughly 5000 square kilometer can be covered with one WiMAX deployment at rough cost of 0.5 million dollars. This would require about 750 to 1000 deployments (of WiMAX MAN’s) to cover all of India’s rural areas. If these wireless networks are augmented with at the least one Identity Service Provider (IDSP) per State (about 20 to 25) in conjunction with a data center that is also a network access point, all such wireless networks can essentially be an Identity enabled Network, allowing for context/profile driven user centric service delivery. Therefore in terms of numbers if we had 5,000 PURA village clusters and approximately 1 WiMAX base station for 5 such village cluster’s we will need about a thousand base station deployments. Certain states would have a larger number of base station deployments based on size (square kilo meters, number of PURA and population distribution) and others might deploy a few. Based on the WiMAX 802.16 technology, multiple deployments can connect with each other using a line of sight microwave link, and therefore negates the need for direct internet connectivity for each of the base stations.
 One datacenter as a network access point can potentially support 20 Wimax station deployments (approximately), with basic services such as Identity Services that offers AAA (authentication, authorisation and access control -plus auditing) for the user population that accesses the network from an entire state for example. That would call for 30 such datacenter distributed across India that offer Network Access Points and foundations services for the WiMAX deployments, such as Identity Services. All WiMAX base station deployments around the nation, can be identity enabled so that connectivity is only provided after successful Authentication and then an Authenticated Session can be established for the Authorisation to Access Specific Services, for Single Sign on within a Circle of Trust (such as a cluster of neighboring PURA’s) and federated between States within India and Government entities offering Services (such as online provident and pension fund tools). However majority of this deployment architecture can be determined based on what is being learnt from the 5 pilots. There are 28 states and seven union territories in India that needs to be have an Identity enabled Wireless Network. States with huge populations (above 50 million) Andhra Pradesh, Gujarat. Karnataka, Madhya Pradesh, Mahrashtra, Rajastan, Tamil Nadu , Uttar Pradesh and West Bengal may potentially have 2 or more datacenter as an Identity Service Provider (IDP) and Network Access Point (NAP), to supports its population, in multiple cities within the state. If Disaster Recovery is taken into account, all the States would have at the least 2 redundant datacenter to protect against natural disasters. Smaller union territories could potentially share the data centers offered by a neighboring state. This ratio of 5 PURA’s to 1 WiMAX base station and 20 base stations to 1 data center with a Network Access Point will also be influenced by the density of the population. For example West Bengal, with its 80+ million in population and 90,000 square km, will need approximately 20 Wimax base station, but may still need more than one datacenter, from a Capacity, Scalability, Performance, Workload and Throughput standpoint. Same is true with Uttar Pradesh, 50 WiMAX base stations 250,000 plus square km, yet it might need 4 plus datacenter to support the 170+ million people. A careful analysis of the throughput requirements of each base station deployments will be needed to support and sustain millions of concurrent connections. Even if we assume that 1 percent of the population attempt to connect online and access services at the same point in time.
One datacenter as a network access point can potentially support 20 Wimax station deployments (approximately), with basic services such as Identity Services that offers AAA (authentication, authorisation and access control -plus auditing) for the user population that accesses the network from an entire state for example. That would call for 30 such datacenter distributed across India that offer Network Access Points and foundations services for the WiMAX deployments, such as Identity Services. All WiMAX base station deployments around the nation, can be identity enabled so that connectivity is only provided after successful Authentication and then an Authenticated Session can be established for the Authorisation to Access Specific Services, for Single Sign on within a Circle of Trust (such as a cluster of neighboring PURA’s) and federated between States within India and Government entities offering Services (such as online provident and pension fund tools). However majority of this deployment architecture can be determined based on what is being learnt from the 5 pilots. There are 28 states and seven union territories in India that needs to be have an Identity enabled Wireless Network. States with huge populations (above 50 million) Andhra Pradesh, Gujarat. Karnataka, Madhya Pradesh, Mahrashtra, Rajastan, Tamil Nadu , Uttar Pradesh and West Bengal may potentially have 2 or more datacenter as an Identity Service Provider (IDP) and Network Access Point (NAP), to supports its population, in multiple cities within the state. If Disaster Recovery is taken into account, all the States would have at the least 2 redundant datacenter to protect against natural disasters. Smaller union territories could potentially share the data centers offered by a neighboring state. This ratio of 5 PURA’s to 1 WiMAX base station and 20 base stations to 1 data center with a Network Access Point will also be influenced by the density of the population. For example West Bengal, with its 80+ million in population and 90,000 square km, will need approximately 20 Wimax base station, but may still need more than one datacenter, from a Capacity, Scalability, Performance, Workload and Throughput standpoint. Same is true with Uttar Pradesh, 50 WiMAX base stations 250,000 plus square km, yet it might need 4 plus datacenter to support the 170+ million people. A careful analysis of the throughput requirements of each base station deployments will be needed to support and sustain millions of concurrent connections. Even if we assume that 1 percent of the population attempt to connect online and access services at the same point in time.

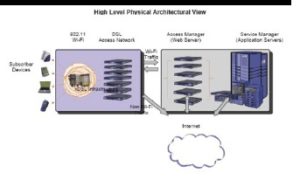
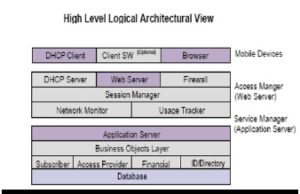
Identity Systems and Access Mangers have been integrated with Wifi base stations (Access Controller) and the same approach has been taken successfully to integrate with WiMAX base stations, as well. A high level physical architecture of the Integrated solution, as well as a logical architecture is described below.
In the high level physical architecture, it is clear that components of an Identity System, such as access manager policy agents, access manager, federation manager, identity manager, replication services, directory servers, etc., are all mostly horizontally scalable, making it the right candidates for a COTS (Commercially-off-the-Shelf) hardware solutions. In the high level logical architecture we see for example a DHCP client and a DHCP server, one can add other such clients and server protocol stack as well; such as the a SIP/IMS client and SIP/IMS Server if there are requirements to go the IMS (IP multi media system route), WiMAX compact SIP client and server, and more. The architecture is extensible with this approach to integration and is scalable as well. A high level physical architecture of the Identity System that can support 20 plus WiMAX base station deployments from One Data Center that offers the network access point, is depicted below. Since each Identity System deployment would support multi-million subscribers and identities it is imperative that the deployment architecture is scalable and highly available as well.
 Long term strategic Benefit
Long term strategic Benefit
• Secure access to the Network (including Bio-Metric support)
• Common Security Framework for multiple Network types and Network Services, including;
• Sensory Networks
• Programmable Networks
• IP based Core Network (IMS)
• WiMAX and WiFi Networks (access networks)
• Multi-media Services
• NG IN Services
• OAM&P Services
• Web Services,
• Entertainment/Video Services and more,
• Integrated and enhanced access to government services via an Identity enable eGov Portal.
• Secure access to individualized documents and forms (land records, tax & insurance docs, employment advertisements and employment application forms, etc.).
• Identity Systems offers the foundation for Open DRM Solutions (user centric) and Content delivery (IPTV, VOD, Digitized education content, etc,).
•Identity Systems based ESB Services (orchestration and choreography of services) within and between circles of trust established in the Center and State.
• Identity Centric eGOV initiatives -such as ePassports, eVoting, Health profile, Social Security, etc.
• Profile/Preference based Service Delivery
• Participation with Business Circles of Trusts established in other countries (such as USA)
• Single Sign On and Single Sign Out
• Near Real time Auditing and Compliance
• User Privacy
• User Centric workflow and interventions
• Secure access to Services
• Glue between the Network layer and the Services Layer (& Control Layer)
• Secure collaboration and participation between States and Programs (through Federation)
Conclusion
A National Identity Initiative forms the foundation for multiple community creation (farmers within a PURA cluster, students belonging to a PURA cluster, dentists within a PURA region, etc), allowing for secure multimedia communication which in turn enhances the mode of collaboration improving commerce and secure delivery of digital content. It acts as the common security framework not just validating identity of users, but also, documents/ forms, services, web sites, devices network elements and sensory equipment.
Majority of the Countries of the world have embarked on a National Identity initiative for these very same reasons. Identity Initiative lays the foundation for
Communication,
Collaboration,
Commerce,
Content and
Communities. 
 Government Initiatives for WiMAX in India
Government Initiatives for WiMAX in India
Several India state governments and city municipalities have announced state/city-wide wireless networks in an alliance between the government bodies and a private partner. Some of them are:
• The Pune Municipal Corporation PMC has announced the “Unwire Pune” project, with Intel Technologies Ltd. as the chief technology and program management consultant. This project is aimed at making 400 sqKms of the city alongwith adjacent areas of Pimpri and Chinchwad wireless. Intel would be deploying the Wi-Fi and WiMax technologies for making the city wire-free. (Reference: http://www.egovpmc.com/ about/about.asp )
• The Uttaranchal government has reportedly had an alliance with Intel and a WiMax pilot project, as a backhaul connectivity model for the state is being worked upon. (Reference: http://www.efytimes.com/fullnewsp.asp?edid=7098 )
• Rajasthan has gone ahead and signed a MoU with Motorola in February 2006 making it first statewide deployment of wireless broadband infrastructure. The MOTOWi4 canopy network will provide for a wireless backbone grid system. (Reference: http://www.connectwithcanopy.com/index.cfm?canopy=spotlight.story&aid=393 )
• The Madhya Pradesh state government has signed the MoU in November 2006 with Motorola and Teledata Informatics as private partners for a wireless network. This project will provide broadband connectivity to rural areas. The villages will be connected to district headquarters and Bhopal. The revenue from the contract is expected to fetch INR 600million annually. The initial contract is set for a period of five years. (Reference: http://www.wirelessiq.com/content/newsfeed/8804.html )
Be a part of Elets Collaborative Initiatives. Join Us for Upcoming Events and explore business opportunities. Like us on Facebook , connect with us on LinkedIn and follow us on Twitter, Instagram.
"Exciting news! Elets technomedia is now on WhatsApp Channels Subscribe today by clicking the link and stay updated with the latest insights!" Click here!





















