“Once you have the master data and the unique IDs are created, you can use it for any kind of application starting from any kind of rural development applications, civil supplies, passport, employment, over all national security projects and the implications are huge, even the ministry of finance, department of income tax everywhere it is required”, says SPS Grover, Vice-President -Sales, Oracle India, (s.grover@oracle.com), in an interview with egov magazine
“Once you have the master data and the unique IDs are created, you can use it for any kind of application starting from any kind of rural development applications, civil supplies, passport, employment, over all national security projects and the implications are huge, even the ministry of finance, department of income tax everywhere it is required”, says SPS Grover, Vice-President -Sales, Oracle India, (s.grover@oracle.com), in an interview with egov magazine
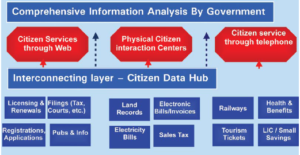
What are the aims and objectives behind the citizen data hub?
The key objective is to integrate various government processes and the key entity for the government is its citizens. There are two ways of doing this. One is that you can have a quick enterprise resource planning solution for the government. This is an end-to-end solution, where everybody works on the same system so that citizens’ information gets transferred, from one department to another. This is not practical and therefore one of the best ways for effective integration across various departments is to bring the permanent citizen data hub in one place, which can then be used by different entities across the country to provide a uniform service experience to the citizens. The data hub also needs to be secured to safeguard citizens’ data.
Which are the countries this is in operation currently?
Different countries have achieved this kind of an objective in a different way. Some countries have social security numbers, and they have used different technologies to achieve this objective. Citizen data hub or the product we brought out is based on our experience of working with some of the world’s large organisations bringing the metadata together– and this is applicable to both, government organisations and enterprise customers. Our government entities are spread across multiple locations, so the task is to bring these entities together. So we thought of two products, one is the customer data hub, which caters to the enterprise customers and the other is the citizen data hub for the government sector.
How does the citizen data hub function and what are its applications in the public sector?
It has the ability to create meta data depending on the data available, which may be required for the citizens and its various attributes. That means during the life cycle you can continue to add more attributes without having to change the complete schema and you can bring data in from various sources and duplicate it and create the master data and continue to populate it onto various systems. The Citizen Data Hub has a hub and spoke architecture that means it can synchronize consistent customer data and processes across the enterprise. For example, if a change happens in one spoke, it is sent to the hub, which is then replicated across the different spokes. And if any spoke does not want any replication, it can check with the hub for the necessary data. Once you have the master data and the unique IDs are created, you can use it for any kind of application starting from any kind of rural development applications, civil supplies, passport, employment, over all national security projects etc. The implications are huge and can be used even by the Ministry of Finance, Department of Income Tax among others.
Please tell us something about how secure this solution is, especially for governments who need to keep the sensitive data secure?
What we provide is technology infrastructure. This means our technology can enable the collection of data, duplication of data, providing unique IDs and all those things in a secure environment. A lot of policies are associated with this, which are beyond the purview of technology deployment. As far as the protection of the data is concerned, all the security validations are built on the Oracle database and the data is only meant to be available to people on a need basis. Security is embedded in the whole infrastructure. Technology features that are necessary in managing such kind of sensitive data is in-built in our infrastructure environment.
What are the plans to work in partnership with Indian government in implementing National ID project through Data Hub solution of Oracle?
We are already working with the National Informatics Centre. I be- lieve the necessary electoral data is being loaded into the system to initiate the process of removing duplication. Oracle is the technology provider and our involvement is to provide technology to users like Department of Information Technology, National Informatics Centre etc. Oracle provides robust and scalable technology to enable e-Government application deployments.
 What future plans does Oracle have for increasing its Government IT market share in India?
What future plans does Oracle have for increasing its Government IT market share in India?
Oracle India is active in the government segment and has partnered with the Indian government in various projects Oracle is carrying out eGovernance projects in all 28 States in India and has more than 100 live government projects. The Government of Uttaranchal is using the Citizen Data Hub and we are providing solutions through our Government Centre of Excellence (CoE).
Are you also working on technology solutions that will have compatibility between the Central data and State data ?
We are working with government agencies on different aspects of e-Government deployments at the Central and State levels. How the data is used and shared between the Centre and State can be answered best by the respective government .
McAfee, Inc. has released its second issue of Sage, a semiannual security journal designed to update and inform technical personnel and security executives on cutting-edge topics that can help them make better informed security decisions. The new issue of Sage includes articles from McAfee researchers, managers and evangelists, on topics including cybercrime, Microsoft Windows Vista security, spyware, spam, cell phone security, data leakage and security risk management. Some of these are summarised below:
- The Future of Cybercrime: Cybercrime follows money. Today, the majority of cybercriminals target PC users, but we can expect more attackers to branch out to other areas of technology, such as voice over internet protocol and radio frequency identifications (RFID), as those technologies become more widely adopted.
- Securing Applications: Application security is continual race and developers are struggling to keep up. As more information comes to light about the nature of computer software bugs and how they might be exploited, hackers can apply this information to their discovery process and find vulnerabilities previously considered secure.
- The Future of Security, Vista Edition: While Microsoft has taken steps to make the base of Microsoft Windows Vista more secure, the improvements both weaken thirdparty efforts to secure systems and don’t go far enough to do the job alone.
- Spyware Grows Up: Although programmers add some security measures during development, new spyware technology often far surpasses the best planning of even the most diligent engineers, opening new fronts of attacks. Spyware will follow us into new technologies, such as Bluetooth and RFID.
- Emails Spam Plague Persists: McAfee expects to see very little increase in the percentage of spam volume over the next two years, but overall spam volume will increase as worldwide bandwidth grows. Image spam is the latest way for spam writers to dodge defenses.
- Online Crime Migrates to Mobile Phones: While current mobile phone service is generally considered safe, McAfee is seeing a rapid growth in mobile attacks with increasingly technical diversification.
- Closing the Data Leakage Tap: Data Leakage is an emerging security concern and has an enormous impact on the reputation of a business. While drive encryption is the only preventative technology that’s reasonably mature, McAfee expects that basic data leakage prevention and disk encryption will be fairly ubiquitous in regulated enterprises within the next five years.
- Managing Risk: Security risk management is an important strategy issue for IT managers. Organisations that fail to select a risk management process, and resign themselves to reactive threat management, will find that the businesses they are chartered with protecting will sail on without them.
Sage is available for download through the McAfee Threat
Center: http://www.mcafee.com/us/threat_center/default.asp.
Be a part of Elets Collaborative Initiatives. Join Us for Upcoming Events and explore business opportunities. Like us on Facebook , connect with us on LinkedIn and follow us on Twitter, Instagram.
"Exciting news! Elets technomedia is now on WhatsApp Channels Subscribe today by clicking the link and stay updated with the latest insights!" Click here!