Foreseeing the necessity of secure access world for the Indian government, ABM has now raised the curtain for its new offering – Cyber Security. The major products into this segment are ‘Instasafe Secure Access’ and ‘Safehats’.
 It is now a well-known fact that as India is moving with high pace towards the digital world, the vulnerability of data is also increasing at the same pace and time. Although this world is revolutionising itself to be smarter than before in every aspect but aren’t we forgetting something? We are embracing changing data driven technologies rapidly but are we accepting the safe and secure ones? Yes, the safe and secure data has now become the oxygen for all data driven technologies.
It is now a well-known fact that as India is moving with high pace towards the digital world, the vulnerability of data is also increasing at the same pace and time. Although this world is revolutionising itself to be smarter than before in every aspect but aren’t we forgetting something? We are embracing changing data driven technologies rapidly but are we accepting the safe and secure ones? Yes, the safe and secure data has now become the oxygen for all data driven technologies.
We hear about all kinds of worrisome news related to malware, spams, hacking and ransomware these days which is definitely a serious warning sign that these games of risk can become big someday and our data may become prey to it crippling the data driven ecosystem.

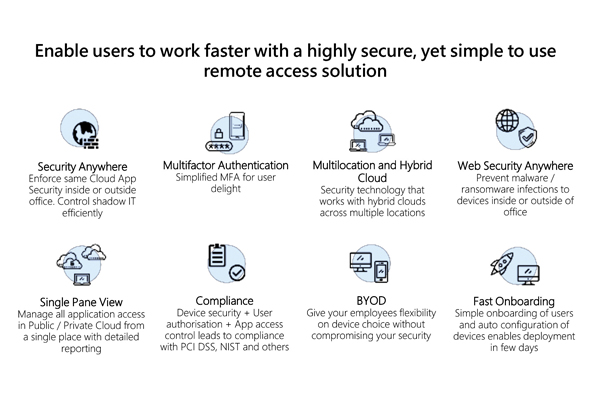
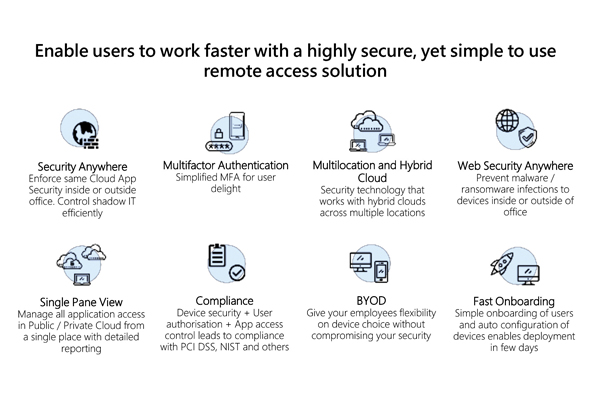
To come out of all these attacks and game of risks, ABM has already committed itself to give a safe and secure environment for the Indian government and other corporates such that there may be significantly less worry in future for their data. It enables users to work faster with a highly secure, yet simple to use remote access solution.
 ABM subsidiary ‘Instasafe Technologies’ is a leading Cloud based Security-as-a-Service solution provider delivering comprehensive and uncompromising protection to mobile and remote workers enabling them to safely and securely access enterprise apps, email and web from anywhere on any network. The most essential products are:
ABM subsidiary ‘Instasafe Technologies’ is a leading Cloud based Security-as-a-Service solution provider delivering comprehensive and uncompromising protection to mobile and remote workers enabling them to safely and securely access enterprise apps, email and web from anywhere on any network. The most essential products are:

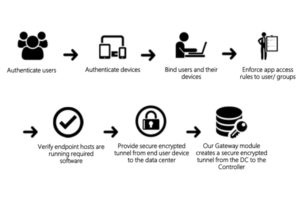
InstaSafe Secure Access – (A Next Generation Cloud Based Secure Access Solution) – InstaSafe Secure Access solution provides an identity based granular access control solution based on the principles of Software Defined Perimeter (SDP). SDP concepts have been derived from the military, especially the Defense Information Systems Agency (DISA), where every device is pre-attested before it can ‘connect’ to the network followed by verification of the identity of the user using MFA (Multi-Factor Authentication) leading to knowing exactly what device was being used and by whom to access the application. With the device and user’s knowledge, we are able to ensure that the device and the user are able to only ‘see’ and ‘access’ the data, that they have ‘prior approval’ to see or access – the ‘need-to-know’ access model.
InstaSafe Secure Access works by having a client agent on the user’s device that helps to connect the user to the controller, where the user is authenticated and the device is verified; and have an agent running in the data center to connect to the Controller and tunnel all user traffic to the data center applications. The InstaSafe Secure Access cloud based Controller performs the following functions:
 SafeHats–(Managed Bug Bounty and Vulnerability Coordination Platform) – The SafeHats Launchpad platform connects security conscious Enterprises, financial institutions and Governments with the WhiteHat hacker community to have their products tested against vulnerabilities. SafeHats is a similar marketplace platform where one side there are enterprises that want to do security testing of their application and another side there are Security researchers/Ethical Hackers who work as on-demand basis and perform security penetration testing of the application. These registered ethical hackers are bound by the confidentiality agreements with SafeHats to maintain the secrecy and assurance to the companies they work for to evaluate any vulnerabilities. Apart from that organisations also can have separate confidential or NDA signed with the registered hackers prior to signing them any testing work.
SafeHats–(Managed Bug Bounty and Vulnerability Coordination Platform) – The SafeHats Launchpad platform connects security conscious Enterprises, financial institutions and Governments with the WhiteHat hacker community to have their products tested against vulnerabilities. SafeHats is a similar marketplace platform where one side there are enterprises that want to do security testing of their application and another side there are Security researchers/Ethical Hackers who work as on-demand basis and perform security penetration testing of the application. These registered ethical hackers are bound by the confidentiality agreements with SafeHats to maintain the secrecy and assurance to the companies they work for to evaluate any vulnerabilities. Apart from that organisations also can have separate confidential or NDA signed with the registered hackers prior to signing them any testing work.
Be a part of Elets Collaborative Initiatives. Join Us for Upcoming Events and explore business opportunities. Like us on Facebook , connect with us on LinkedIn and follow us on Twitter, Instagram.











