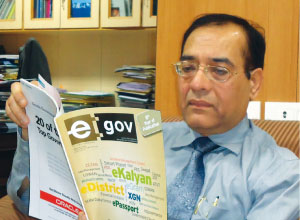
 Dr Gulshan Rai, Director General, Computer Emergency Response Team – India (CERT-In) talks to Dr Rajeshree Dutta Kumar and Anand Agarwal, and touches upon a wide range of issues related to security in the ICT domain
Dr Gulshan Rai, Director General, Computer Emergency Response Team – India (CERT-In) talks to Dr Rajeshree Dutta Kumar and Anand Agarwal, and touches upon a wide range of issues related to security in the ICT domain
I’d start by requesting you to share with us the mandate that CERT-In has, and the activities your organization is involved in, in the cyber security domain.

CERT-In draws its mandate from Section 70 (B) of the Information Technology Act, 2000. The mandate includes the collection of information pertaining to cyber incidents, issue vulnerability notes, advisories, White Papers, the analysis of those incidents and then advising to the users all over the country about the security breaches and what threat is persisting, what threats are likely to come there. These are the basic mandates and are carried out through different modes, different ways, by interacting with the public parties, by interacting with the users group be it public, private, govt. or academia. We take their help and a lot of incidents are reported by them. We analyse threats ourselves and also take their help. We also take help from the international agencies who are in touch with us. The prime responsibility of CERT-In is to analyze the incidents and to provide emergency response to the users, organizations in the country and outside.
If we were to classify your functions into proactive and reactive parts, what functions would come into the proactive security provisions for the cyber assets the country has and what are the reactive measures?
The CERT computer emergency response team is the nodal agency in the area of emergency response team in the country. Every country has one and we are the national agency for India. When we talk about reactive manner, it means incident happens and we analyze incidents and recover from the incidents and then tell the users that these are the steps you need to take in future.

When we talk about proactive part, based on our experience and on the international scenario, we take steps in advance – proactively – so that the systems and IT infrastructure at the user and organisations’ level or the government is kept secured. There are many preventive or proactive steps. Firstly, we issue the advisories, we issue the vulnerability notes. Then we issue the white papers bringing out different technologies and different vulnerability or the different threats that technology has. We have around 800 contracts throughout the country, with Chief Security Officers (CSOs), who are distributed among public and private sectors, academia and government. We regularly conduct trainings for them, exposing them to different emerging threats, different security breaches, what solutions have been implemented, what they can do, what technology they can deploy etc. We also train police officials on cyber forensics.
The third proactive thing that we do is conduct is the cyber drills, each of which is done with a specials group. We have conducted five drills so far, and are going to conduct one more in March. We have conducted drills with the power sector, financial sector, banks and insurance companies, with the government, with ISPs and also with general industry bodies such as FICCI, NASSCOM, CII etc. We also conduct drills internationally. Our participation in the past has been highly appreciated at international forums such as the Asia Pacific Forum of CERTs.
“We work 24X7 and our working is very transparent”
We also help the user organisations to implement the best security practices. We provide online testing, test their security practices, perform selective audit of systems and access their systems from here with their permission. Every user is advised through our web as to what steps need to be taken or how we can interact with this. We work 24X7 and our working is very transparent.
We now see more and more government functions moving online. Paper-based exchanges are now being replaced by email and the IT Act makes these legally valid documents. So, how well placed is the Government of India and governments of various states when it comes to security of this valuable national information that is present online? We keep coming across reports that our systems have been targeted by hacker groups, by outside powers…
There is a proliferation of Information Technology and the e-Governance plan is very ambitious and we have moved quite a way forward in implementing various applications. When it comes to the larger projects, there is quite a high level of security awareness in terms of securing information or securing infrastructure and when these projects are implemented, infrastructure security is getting inbuilt into the implementation part of it. For example, look at NIC – they have been strengthening their infrastructure very significantly. We also circulate monthly bulletins and expose them to the threats that are coming and the steps that need to be taken over it and those steps are being implemented by many large organizations. Security infrastructure is getting implemented with the general infrastructure. The states are aware about it, concerned about it, are being trained, are being exposed to that. But one thing needs to be recognised is that there can never be 100 percent security.
There are some issues in terms of manpower, and in terms of awareness, things are looking to be more positive but we have to do that, we have to be very careful. The whole issue is categorized by the options in the technology, new technology comes up, new software comes up, and one has to really be on the toes to counter the emerging threats. Of course, many things still need to be done, but overall, we are moving in the right direction.
Do we have an IT Security Policy for the private sector? Do we have one for the government sector?
I think there are couple of issues here. The Draft IT policy has been up on the web in March 2011 and lot of comments have come. These comments are being analysed and major government departments have given very significant comments on the policy and we are on the verge of finalising the policy and I think before the end of the financial year, the policy will be in place.
In addition, the 2008 Amendment to the IT Act introduced Section 43A, which is primarily intended to enhance provisions related to data security and data protection. Section 43A requires the body corporates to maintain and implement the reasonable best security practices, protect the sensitive private information. It lays down procedures for handling of this information and data transfer etc.
The Rules under this Section were notified in February 2011. The victim whose information has been stolen or whose system has been compromised, is now entitled to get compensationfrom the body corporate, commensurate to the damage. Then, there is section 72A, where any user or any victim can file a case for leakage of information or for breach of contract. So that gives a criminal protection to the persons whose data is compromised.
The laws have been strengthened, the implementation is now underway. It will take some time, as training people is a lengthy process. More or less we are on the right path. Europe hasrecently come out with a Data Protection Act. If you look at their policies, many of those provisions are already present in our IT Act and Rules.
What kind of security challenges would shift to the clouds and shift to mobile governance sphere entail, and how are we going to meet them?
These things are being discussed. In my view, the issues right now are primarily more of a legal nature. Only then would the security aspects come up. So far, no country has implemented a true government cloud, due to complex legal issues. A number of best practices need to be evolved to address the security and legal challenges. I think there is no single understanding of legal and security aspects and that is the reason why no true cloud has been implemented.
How is the government going to balance the need for ensuring privacy and at the same time not compromise on national security?
There are three aspects to this debate, and these are similar to the three vertices of a triangle. You have privacy, you have security, and the third aspect is the right to information. So if you want to have privacy, you compromise on security, you compromise the right to information and vice versa. So we have to strike a balance and for that, lot of maturity and awareness has to come among the citizens in the country or worldwide. The three aspects are connected but we need to draw a line. We should know what we need to do.
So who gets to draw that line? That’s the key question here.
This is not the issue that has remained with the government. Government is one important stakeholder. Society is a key stakeholder. We have to come to a certain level of understanding. It is a complex area. Today you talk about cloud computing, today you talk about the Internet, how do such technologies impact privacy? How do you do that? Technology is changing the entire paradigm, whether you talk about security or privacy. The very complex matrix can be defined, understood and can be implemented only once we all be mature, sit together and find a solution and follow discipline.
Be a part of Elets Collaborative Initiatives. Join Us for Upcoming Events and explore business opportunities. Like us on Facebook , connect with us on LinkedIn and follow us on Twitter, Instagram.











